Your smartphone used to be a simple tool for staying in touch. Today, it has become one of the most targeted gateways for cybercrime, with SMS phishing and AI-powered scam messages evolving at an alarming pace.
Across global markets, attackers are leveraging generative AI to craft natural, context-aware conversations, while fake base station attacks and infrastructure-level exploits are bypassing traditional carrier filters. At the same time, governments, telecom operators, and platform providers are racing to reinforce defenses with new technical standards and regulatory frameworks.
In this article, you will explore how Android’s messaging ecosystem is responding in 2025. From on-device machine learning in Google Messages and Gemini Nano-powered scam detection to RCS with verified sender authentication and end-to-end encryption, we break down the technologies, data, and real-world countermeasures shaping the future of secure mobile communication. If you care about gadgets, privacy, and the next generation of messaging protocols, this deep dive will give you the strategic insight you need to stay ahead.
- The Evolution of Smishing: How Generative AI Eliminated the Red Flags
- Conversational Scam Campaigns and the Rise of AI-Driven Social Engineering
- Fake Base Stations and Infrastructure-Level SMS Attacks
- Why SMS Is Structurally Insecure: Protocol Limitations from the 1990s
- Inside Google Messages: On-Device Machine Learning and TensorFlow Lite
- Gemini Nano and Context-Aware Scam Detection on Android
- Privacy-Preserving Hashing and Crowd Intelligence with SimHash
- Google Safe Browsing and Real-Time URL Protection in Messages
- RCS vs. SMS: Protocol-Level Security, Encryption, and IP-Based Authentication
- Verified Sender and RCS Business Messaging: Ending Brand Impersonation
- End-to-End Encryption in RCS and Its Security Implications
- Carrier Strategies in Japan: +Message, Google Jibe, and Rakuten Link
- iOS 18 and RCS Adoption: Cross-Platform Security Breakthrough
- Government Action and Opt-In Regulation: Legal Pressure on SMS Abuse
- Advanced Defense Strategies for Power Users: Passkeys, Authenticator Apps, and Layered Protection
- 参考文献
The Evolution of Smishing: How Generative AI Eliminated the Red Flags
For years, one of the easiest ways to spot a smishing attempt was awkward language. Strange kanji choices, unnatural phrasing, or clumsy machine translation acted as built‑in alarms. That assumption no longer holds. Generative AI has erased the linguistic fingerprints that once exposed fraud.
As Japan’s Ministry of Internal Affairs and Communications has noted in recent policy discussions, large language models now enable the mass production of fluent, contextually appropriate Japanese. What once required a native speaker or expensive localization can now be automated at scale. The result is Smishing 2.0: persuasive, adaptive, and disturbingly human.
Security researchers are also observing a shift in structure, not just style. According to Google’s security team, recent Android scam detections show attackers initiating seemingly harmless conversations before introducing malicious intent. The red flag is no longer in the grammar, but hidden in the progression.
| Aspect | Traditional Smishing | AI-Driven Smishing |
|---|---|---|
| Language quality | Often unnatural or mistranslated | Native-level fluency |
| Delivery style | Mass URL blast | Conversational engagement |
| Detection trigger | Keyword spotting | Behavioral and contextual analysis required |
The most dangerous evolution is the rise of long-game conversational scams, sometimes compared to “pig butchering” tactics documented by global cybersecurity analysts. An initial message may read, “Hi, is this Tanaka-san? It’s been a while.” When the recipient replies that it’s a mistake, the attacker apologizes and continues casually. AI systems sustain these exchanges for days or weeks, gradually building trust before pivoting to investment schemes or malicious app links.
This approach neutralizes traditional spam filters built on static keywords such as “urgent,” “payment,” or “reward.” Instead of triggering immediate suspicion, the attacker exploits social norms—politeness, curiosity, and reciprocity.
Data cited in Japan’s Information Security 10 Major Threats 2025 report shows that financial demands via email and SMS remain a persistent and high-impact threat category. What has changed is efficiency. Generative AI reduces the marginal cost of personalization to near zero, enabling attackers to tailor tone, region-specific references, and even time-of-day phrasing automatically.
Equally concerning is adaptive iteration. If a victim hesitates, the AI can instantly reformulate its pitch, soften urgency, or introduce fabricated testimonials. This real-time refinement mirrors legitimate customer engagement tools used in marketing automation—except deployed for deception.
For gadget-savvy users who once relied on spotting linguistic awkwardness, the battlefield has shifted. Detection now depends less on surface anomalies and more on understanding intent patterns, escalation timing, and cross-channel consistency. The disappearance of obvious red flags does not signal reduced risk—it signals a smarter adversary.
Conversational Scam Campaigns and the Rise of AI-Driven Social Engineering

Conversational scam campaigns have fundamentally changed the economics of smishing. Instead of blasting millions of identical messages, attackers now invest in dialogue. The goal is no longer a single click, but a gradual erosion of skepticism. Generative AI has made this shift scalable, allowing fraudsters to simulate patience, empathy, and cultural nuance at near-zero marginal cost.
According to Google’s security team, recent Android protections specifically target so-called “conversational scams,” where an initial harmless message—such as a mistaken greeting—evolves into investment pitches or requests for money. This mirrors the broader “pig butchering” model documented by international law enforcement, where trust-building precedes financial exploitation.
| Traditional Smishing | Conversational Scam | Security Impact |
|---|---|---|
| Mass, identical messages | Personalized, adaptive dialogue | Harder to flag via keyword filters |
| Immediate malicious link | Delayed payload delivery | Evades URL-based detection |
| Language errors common | AI-polished native fluency | Removes “unnatural phrasing” red flags |
The Ministry of Internal Affairs and Communications in Japan has warned that generative AI enables the rapid production of natural Japanese text, weakening traditional detection methods based on linguistic anomalies. What once exposed overseas fraud rings—awkward grammar or mistranslated idioms—has largely disappeared.
This evolution also exploits human psychology more precisely. Reports from IPA’s Information Security 10 Major Threats highlight that financial extortion via email and SMS remains persistently ranked among top risks. The success of conversational scams lies in their timing: attackers wait until emotional rapport is established before introducing urgency or exclusivity.
Machine learning models can analyze response patterns in real time. If a target replies cautiously, the tone softens. If curiosity is detected, the script accelerates toward investment opportunities or crypto transfers. This adaptive flow resembles customer relationship management systems—except optimized for fraud.
Moreover, conversational campaigns reduce operational risk for criminals. By avoiding suspicious keywords early on, they bypass carrier-level filtering and on-device spam classifiers tuned for obvious phishing markers. Only after trust is built does the malicious vector—malware link, payment request, or app installation—appear.
The rise of AI-driven social engineering signals a strategic pivot: from technical exploitation to cognitive exploitation. Firewalls and filters still matter, but the primary battleground has shifted to perception, trust, and behavioral influence—areas where large language models now operate with unsettling effectiveness.
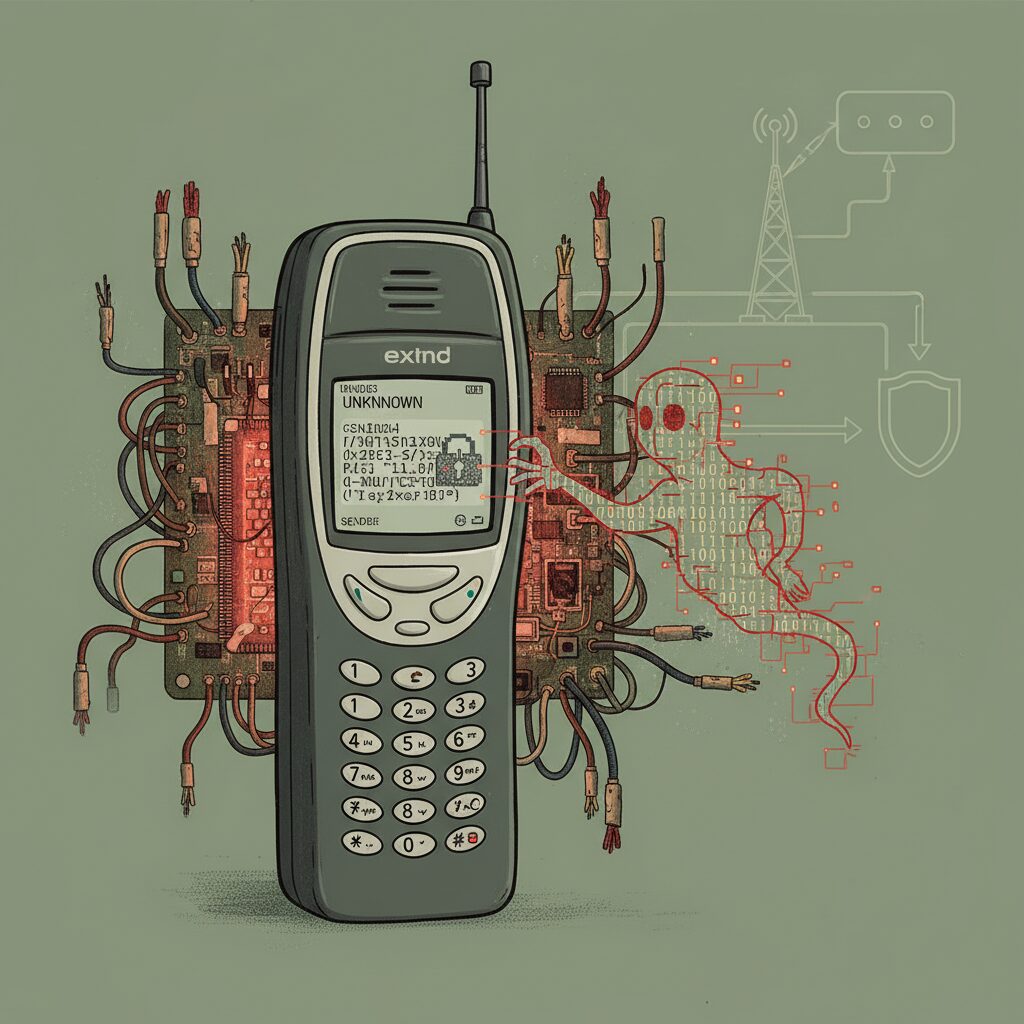
Fake Base Stations and Infrastructure-Level SMS Attacks
While AI-driven filtering operates at the device level, fake base stations attack the problem at its physical root. Instead of tricking algorithms, attackers manipulate the radio layer itself. This infrastructure-level threat has become a tangible concern in urban Japan since 2024, as reported by industry outlets such as CommsRisk and echoed by domestic carriers.
These devices, often referred to as IMSI catchers or SMS blasters, mimic legitimate cellular base stations. Smartphones are designed to connect to the tower with the strongest signal. When a rogue transmitter broadcasts at higher power in a crowded district, nearby devices may automatically latch onto it without any visible warning.
The critical danger is that messages injected through a fake base station can bypass carrier-level spam filters entirely.
Under normal circumstances, SMS traffic flows through the carrier’s core network, where filtering systems inspect sender patterns, URLs, and known malicious signatures. However, when a device is temporarily camped on a rogue cell, the attacker can push SMS messages directly to the handset over the radio interface. Because the carrier’s switching infrastructure is never involved, network-based screening mechanisms are effectively sidestepped.
Japanese telecom operators including NTT Docomo, KDDI, SoftBank, and Rakuten Mobile publicly warned users in 2024 about smishing campaigns linked to suspected fake base stations operating in metropolitan areas. According to those alerts, messages often impersonated the carriers themselves, exploiting brand trust to prompt users to click phishing links.
| Layer Targeted | Conventional Smishing | Fake Base Station Attack |
|---|---|---|
| Delivery Path | Via carrier core network | Direct radio injection |
| Carrier Filtering | Applied | Bypassed |
| User Visibility | Normal SMS | Indistinguishable SMS |
From a technical standpoint, this attack exploits legacy signaling assumptions in cellular standards. Earlier generations of mobile protocols were not designed with strong mutual authentication between handset and tower in mind. As a result, devices may authenticate to the network, but the network is not always equally authenticated to the device, creating an asymmetry that rogue equipment abuses.
What makes this particularly concerning for gadget enthusiasts is its portability. Modern rogue base station kits can be compact enough to fit inside a vehicle, enabling attackers to move between high-density locations such as train stations or entertainment districts. The attack window may last only minutes, yet that is sufficient to broadcast thousands of phishing messages.
Mitigation at this layer is complex. Carriers coordinate with Japan’s Ministry of Internal Affairs and Communications to identify and shut down unauthorized radio transmissions, but detection requires spectrum monitoring and physical investigation. Unlike cloud-based spam filtering, there is no simple software patch that eliminates the risk overnight.
For users, the key insight is this: infrastructure-level SMS attacks undermine trust not by sophistication of language, but by exploiting the physics of connectivity itself. Recognizing that some threats originate below the application layer reshapes how we evaluate messaging security in 2025. The battlefield is no longer confined to apps and AI models; it extends to the airwaves surrounding your device.
Why SMS Is Structurally Insecure: Protocol Limitations from the 1990s
SMS was standardized in the early 1990s as part of the GSM specification. At that time, it was designed for short, non-critical notifications between subscribers, not for financial authentication or identity verification.
Security was not a primary design goal; interoperability and delivery efficiency were. This historical context explains why SMS remains structurally fragile even in 2025.
According to technical documentation summarized by the GSM Association and security analyses referenced in industry research, legacy SMS relies on the SS7 signaling network, an architecture built on implicit trust between telecom operators.
| Design Element | 1990s Assumption | 2025 Reality |
|---|---|---|
| Network Trust | Operators trust each other | Global interconnection exposes attack surface |
| Encryption | Air interface only | No end-to-end protection |
| Sender Identity | Assumed authentic | Easily spoofed |
First, SMS messages are not end-to-end encrypted. While radio links between handset and base station may use encryption, messages are typically readable within carrier infrastructure. This means confidentiality depends heavily on telecom network integrity rather than cryptographic guarantees.
Second, SS7 was built on a “trusted network” model. Once an entity gains signaling access—legitimately or otherwise—it can query subscriber information or reroute messages. Security researchers have demonstrated for years that SS7 weaknesses enable location tracking and message interception under certain conditions.
This is not a software bug. It is a structural property of the protocol stack.
Third, sender identity in SMS is fundamentally weak. Alphanumeric Sender IDs can be forged in many international routing scenarios. There is no mandatory cryptographic verification tying a brand name to a legally verified entity. As a result, attackers can impersonate banks, logistics firms, or government agencies with minimal friction.
Industry commentary, including analysis cited by Android-focused publications discussing spam trends, repeatedly points out that filtering happens after delivery attempts. The protocol itself does not validate authenticity before a message reaches the user layer.
Another overlooked limitation is store-and-forward architecture. SMS centers temporarily store messages before delivery. While this improves reliability, it introduces additional infrastructure nodes where messages exist in readable form, increasing exposure compared to modern encrypted messaging systems.
Importantly, SMS was never intended for multi-factor authentication at global scale. Yet today it carries one-time passwords for banking, crypto exchanges, and social media logins. The mismatch between original design scope and current security expectations creates systemic risk.
Even improvements at the application layer—such as AI-based spam detection—cannot change these foundational constraints. They mitigate abuse but do not retrofit cryptographic identity or zero-trust validation into the signaling core.
In essence, SMS operates on inherited trust from a telecom era that no longer exists. In a hyper-connected, API-driven, fraud-industrialized world, that inherited trust becomes the weakest link.
Understanding this historical and architectural backdrop is critical. Without recognizing that SMS insecurity stems from protocol-era assumptions, it is easy to mistake modern attacks for temporary spikes rather than predictable outcomes of legacy design.
Inside Google Messages: On-Device Machine Learning and TensorFlow Lite
At the heart of Google Messages’ defense architecture lies a design choice that fundamentally reshapes mobile security: spam detection runs directly on your device. Instead of uploading message content to the cloud for inspection, Google leverages on-device machine learning to analyze SMS in real time while preserving user privacy.
This approach reflects a growing consensus in security engineering. As Google explains in its official documentation, spam protection in Messages uses automated systems that operate locally, meaning message content does not need to leave the phone for classification. In an era of escalating smishing attacks, that architectural decision is not just elegant—it is strategic.
TensorFlow Lite: Edge AI in Your Pocket
The technical backbone of this system is TensorFlow Lite, Google’s lightweight inference engine optimized for mobile and embedded hardware. Designed to run efficiently on CPUs and dedicated NPUs within modern SoCs, TensorFlow Lite enables text classification models to execute in milliseconds without noticeable battery drain.
When an SMS arrives, the model evaluates linguistic signals such as suspicious keyword combinations, structural anomalies, and known spam patterns. Even offline, the classifier can assign a risk score and automatically divert high-probability spam into a filtered folder. According to Android developer documentation, TensorFlow Lite is specifically engineered for low-latency inference on constrained devices, making it suitable for always-on security tasks.
| Component | Role | Security Impact |
|---|---|---|
| TensorFlow Lite | On-device inference engine | Real-time classification without cloud upload |
| Local ML Model | Spam pattern detection | Offline protection against known tactics |
| Device NPU/CPU | Hardware acceleration | Low latency, minimal battery overhead |
This edge-based design is particularly effective against large-scale keyword-driven campaigns. Messages containing urgent financial language or suspicious account-update prompts can be intercepted before the user even sees a notification banner.
From Pattern Matching to Context Awareness
While early mobile spam filters relied heavily on static keyword lists, modern attacks increasingly exploit natural language fluency. Google has publicly detailed new AI-powered scam detection features on Android that expand beyond simple token matching. On supported high-end devices, more advanced on-device models can analyze conversational context, not just isolated phrases.
This matters because contemporary smishing often unfolds gradually. A benign greeting may evolve into a financial request days later. By evaluating shifts in conversational intent, on-device models can surface warnings such as “This message may be a scam,” overlaying alerts without transmitting the conversation to external servers.
All core classification processes occur locally on the handset, minimizing exposure of personal message content while still benefiting from AI-driven protection.
Privacy-Preserving Signal Sharing
On-device detection alone cannot identify entirely new global spam waves. To address this, Google combines local inference with privacy-preserving signal aggregation. Instead of uploading raw messages, systems may transmit non-content signals—such as cryptographic hashes or metadata—when users opt in to spam reporting.
Research from Google on near-duplicate detection and SimHash-style techniques shows how similar documents can be clustered without storing original text. This enables rapid identification of coordinated campaigns while reducing the risk of exposing personal communications.
The result is a feedback loop: local AI blocks immediate threats, anonymized signals strengthen global models, and updated lightweight classifiers are redistributed back to devices. For gadget enthusiasts who care about both performance and privacy, this architecture demonstrates how edge AI and federated intelligence can coexist—turning every Android handset into an active node in a distributed security network.
Gemini Nano and Context-Aware Scam Detection on Android
The evolution from rule-based spam filtering to context-aware AI marks a decisive shift in Android’s defense strategy. With the integration of Gemini Nano into select Android devices, Google Messages moves beyond keyword detection and begins analyzing conversational intent in real time.
According to Google’s official security blog, these new AI-powered scam detection features are designed to identify suspicious patterns in ongoing conversations, particularly those resembling “long con” social engineering tactics. Instead of flagging isolated words, the model evaluates how a dialogue evolves.
This distinction matters because modern smishing campaigns rarely rely on obvious trigger phrases. They simulate authentic human interaction, gradually steering users toward financial manipulation or malicious links.
From Pattern Matching to Intent Recognition
| Detection Layer | Primary Strength | Limitation Addressed by Gemini Nano |
|---|---|---|
| Traditional ML (TensorFlow Lite) | Keyword and structural anomaly detection | Limited understanding of evolving conversation context |
| Gemini Nano (On-device LLM) | Semantic and intent analysis | Detects gradual persuasion and behavioral redirection |
Gemini Nano operates entirely on-device, which is critical from a privacy standpoint. As Google explains in its documentation on spam protection, message content does not need to be uploaded to external servers for analysis. This architecture preserves user confidentiality while enabling advanced AI reasoning.
What makes this powerful is its ability to detect shifts in narrative tone. For example, a seemingly harmless “wrong number” introduction that transitions into investment advice can trigger a contextual risk alert.
The system evaluates progression, not just presence. That progression-based modeling is particularly effective against AI-generated conversational scams that mimic natural rapport building.
Real-Time Warnings Without Cloud Exposure
When suspicious patterns are detected, Android surfaces a contextual warning overlay within the conversation thread. Users are informed that the interaction may be fraudulent and are prompted to exercise caution before sending money or sensitive information.
This approach aligns with findings from the IPA’s 2025 security threat report, which highlights social engineering via SMS as a persistent and growing risk. Traditional filters struggle because the malicious payload often appears only after trust is established.
By running inference locally, Gemini Nano reduces latency and eliminates dependency on network connectivity. Even offline, detection logic remains active.
Another technical advantage is resilience against zero-day scam templates. Because Gemini Nano understands semantic relationships rather than memorizing exact templates, slight variations in phrasing do not easily bypass detection.
This design also mitigates a common adversarial tactic: small textual mutations intended to evade hash-based grouping systems. While hash comparison remains valuable at scale, LLM reasoning closes the gap at the individual device level.
For power users, this means protection no longer depends solely on whether a specific campaign has already been reported globally. Your device can identify suspicious persuasion patterns even if the exact message has never been seen before.
As generative AI lowers the barrier for attackers to craft fluent, culturally natural messages, defensive AI must operate at equal sophistication. Gemini Nano represents that shift—bringing context-aware reasoning directly into the messaging layer of Android.
Privacy-Preserving Hashing and Crowd Intelligence with SimHash
Modern spam detection must balance two conflicting goals: learning from global attack patterns while keeping personal messages private. Google Messages addresses this tension through privacy-preserving hashing techniques such as SimHash combined with large-scale crowd intelligence.
Traditional cryptographic hashes like SHA-256 are designed so that even a one-bit difference produces a completely different output. This avalanche effect is ideal for security, but useless for clustering near-duplicate spam where attackers slightly modify wording to evade filters.
SimHash, a form of Locality Sensitive Hashing (LSH), takes the opposite approach. Similar texts generate similar hash values, enabling systems to group related messages without storing or analyzing the original content in plain form.
Hashing Approaches in Spam Detection
| Method | Behavior | Spam Detection Suitability |
|---|---|---|
| SHA-256 | Completely different output for minor changes | Poor for near-duplicate grouping |
| SimHash (LSH) | Similar output for similar texts | Effective for campaign clustering |
Google Research has long described near-duplicate detection as essential for web-scale indexing, and the same principle applies to messaging. According to published research on SimHash and large-scale duplicate detection, compact fingerprints allow billions of documents to be compared efficiently without exposing raw data.
In practice, when a user opts in to spam reporting, Google Messages does not upload the entire SMS conversation. Instead, it can transmit derived signals such as hashed representations or metadata. The server sees patterns, not private conversations.
This is where crowd intelligence becomes powerful. If thousands of devices independently produce highly similar SimHash values for newly received messages, the backend can infer the emergence of a coordinated campaign. Even if attackers randomize names or minor phrases, the structural similarity remains detectable.
Once a new spam cluster is identified, updated detection models or signatures can be distributed back to devices. Because much of the classification runs on-device, as documented in Google’s privacy explanations for spam protection, the cloud acts as an early-warning radar rather than a surveillance engine.
This architecture is especially critical in regions facing rapidly evolving smishing tactics. When generative AI produces fluent, varied text, keyword-based filtering weakens. However, similarity-aware hashing can still capture shared semantic or structural traits across variants.
From a marketing and platform-trust perspective, this model also protects legitimate brands. If phishing campaigns impersonate a company at scale, clustering via SimHash accelerates detection and takedown, reducing reputational damage.
Ultimately, SimHash and crowd intelligence illustrate a broader shift in mobile security design. Instead of choosing between privacy and protection, modern systems embed mathematical techniques that allow both. For gadget-savvy users, understanding this invisible layer reveals how billions of messages can be analyzed collectively—without turning personal inboxes into open books.
Google Safe Browsing and Real-Time URL Protection in Messages
When a malicious SMS arrives, the most dangerous element is often not the text itself but the URL embedded within it. Google Messages addresses this risk by integrating Google Safe Browsing and real-time URL protection directly into the messaging workflow, creating a defensive layer that activates before a user ever opens a browser.
Google Safe Browsing is the same threat intelligence system used in Chrome and Android to block phishing and malware sites. According to Google’s public security documentation and white papers, Safe Browsing protects billions of devices by continuously maintaining and updating lists of unsafe web resources, including phishing domains, malware distribution points, and social engineering sites. By extending this infrastructure into Google Messages, SMS links are evaluated against a constantly refreshed global threat database.
The key advantage is pre-click protection: links are assessed at the messaging layer, not just after a web page begins to load.
When a message containing a URL is received, Google Messages extracts the link and checks it against Safe Browsing signals. If the domain or specific path is known to host phishing or malware, the system displays a prominent warning and may disable direct interaction with the link. This prevents users from accidentally navigating to credential-harvesting pages that mimic banks, tax authorities, or delivery services.
The protection model can be summarized as follows.
| Protection Layer | Primary Function | User Impact |
|---|---|---|
| Safe Browsing Database | Matches URLs against known phishing/malware lists | Displays warning before site loads |
| Real-Time URL Analysis | Evaluates newly observed or obfuscated links | Blocks emerging scam domains quickly |
| Redirect Resolution | Checks shortened or multi-hop URLs | Prevents short-link evasion tactics |
One critical capability is handling shortened URLs and redirect chains. Attackers frequently use services such as generic link shorteners to disguise malicious destinations. Google’s infrastructure can analyze the redirect path behind such links, identifying the final landing page rather than relying solely on the visible short domain. This significantly reduces the effectiveness of basic obfuscation tactics commonly used in smishing campaigns.
Real-time URL protection becomes especially important in fast-moving phishing waves. As noted in Google’s security blog discussions on scam detection, threat actors often rotate domains rapidly to avoid static blocklists. By leveraging large-scale telemetry and automated threat detection systems, Safe Browsing can flag newly discovered malicious sites and propagate updates quickly across devices. This shortens the window of exposure between the launch of a scam domain and its detection.
From a privacy perspective, Google emphasizes that protections are designed to minimize exposure of personal message content. Rather than uploading entire conversations indiscriminately, the system focuses on URLs and associated security signals. This aligns with the broader Android security model, where on-device intelligence and selective data sharing are used to balance safety with user confidentiality.
The difference between traditional SMS risk and Safe Browsing–enabled messaging is stark. In a legacy scenario, a user taps a link, the browser loads the phishing site, and only then may a warning appear—if at all. With integrated URL protection, the alert can surface directly inside the messaging interface, interrupting the attack chain earlier. Interrupting the attack before the credential entry stage dramatically lowers the probability of account compromise.
Another strategic benefit lies in ecosystem scale. Because Safe Browsing data is shared across Chrome, Android, and other Google services, intelligence gathered from web browsing activity can strengthen SMS defenses. If a phishing campaign is detected via Chrome on desktop, the corresponding domain can be flagged in mobile messaging almost immediately. This cross-surface intelligence fusion creates a unified anti-phishing perimeter.
However, no system is infallible. Brand-new domains used in highly targeted attacks may not be flagged instantly. This is why Safe Browsing is most effective when combined with on-device scam detection models that analyze message context and intent. While URL reputation stops known bad destinations, contextual AI can identify suspicious persuasion patterns even before a link gains notoriety.
For security-conscious users, the takeaway is clear: keeping Google Messages and Google Play Services updated ensures access to the latest Safe Browsing definitions and real-time detection improvements. Threat intelligence evolves daily, and URL-based attacks adapt just as quickly.
In the broader battle against smishing, Google Safe Browsing and real-time URL protection transform SMS from a passive conduit into an actively monitored channel. By embedding web-grade threat intelligence directly into the messaging layer, Android reduces the success rate of phishing campaigns at their most critical junction—the moment between curiosity and click.
RCS vs. SMS: Protocol-Level Security, Encryption, and IP-Based Authentication
At the protocol level, SMS and RCS are fundamentally different in how they establish trust, protect content, and authenticate senders. SMS was designed in the 1990s for circuit-switched networks, primarily using SS7 signaling. It does not natively verify sender identity, nor does it encrypt message content end to end. As a result, spoofed sender IDs and interception risks are structural weaknesses rather than implementation bugs.
RCS, standardized by the GSMA under the Universal Profile, operates over IP networks instead of legacy signaling channels. This architectural shift enables stronger authentication, encrypted transport, and platform-level verification frameworks. The difference is not cosmetic. It changes who can send, who can impersonate, and who can read.
| Layer | SMS | RCS |
|---|---|---|
| Transport | SS7 / circuit-switched | IP (mobile data / Wi-Fi) |
| Encryption | Not end-to-end | E2EE supported (Google Messages) |
| Sender Identity | Easily spoofed | Verified Sender framework |
The absence of built-in sender authentication is the core security flaw of SMS. Attackers can manipulate alphanumeric sender IDs or exploit weaknesses in SS7 routing. Industry analyses and security researchers have repeatedly documented SS7-based interception risks, highlighting that SMS was never engineered for adversarial internet-scale abuse.
RCS mitigates this through IP-based authentication and service-layer verification. When deployed via platforms such as Google’s Jibe Cloud, connections are established through authenticated client sessions tied to SIM credentials and data connectivity. Unlike SMS blasters that rely on radio-layer manipulation, IP-based delivery requires valid network authentication, significantly raising the bar for impersonation.
Encryption is another dividing line. In Google Messages, person-to-person RCS chats use end-to-end encryption, meaning only sender and recipient hold the keys. According to Google’s security documentation, even the service provider cannot read message content when E2EE is active. SMS, by contrast, remains readable within carrier infrastructure.
For business messaging, RCS introduces Verified Sender mechanisms. Enterprises must undergo vetting before registering brand assets such as logos and display names. The authentication process links a verified legal entity to a messaging profile. This transforms identity from a text string into a cryptographically and contractually bound credential.
The practical implication is decisive: in SMS, identity is declarative; in RCS, identity is validated. In SMS, encryption is incidental; in RCS, it is protocol-aware. In SMS, transport relies on legacy signaling; in RCS, it leverages authenticated IP sessions.
For security-conscious users and enterprises alike, the protocol shift represents more than richer media support. It marks a transition from trust-by-assumption to trust-by-design, where authentication, encryption, and network-layer validation are embedded into the communication stack itself.
Verified Sender and RCS Business Messaging: Ending Brand Impersonation
Brand impersonation has long been the structural weakness of legacy SMS. Because traditional SMS lacks a built-in sender authentication framework, attackers can spoof alphanumeric sender IDs or phone numbers with minimal friction. This technical gap is precisely what Verified Sender and RCS Business Messaging (RBM) are designed to eliminate.
According to Google’s Business Communications documentation and GSMA materials, RBM introduces a mandatory vetting process before a brand is allowed to message users. In other words, identity verification is no longer optional marketing hygiene but a protocol-level requirement.
Verified Sender shifts trust from visual guesswork to cryptographic and procedural validation. Users no longer rely solely on message tone or wording to judge legitimacy.
The verification flow typically includes legal entity validation, domain and number ownership confirmation, and compliance checks performed by carriers or approved aggregators. Only after passing this process can a business register its official brand profile within the RCS ecosystem.
That profile is not cosmetic. It enables structured brand elements to appear natively inside the messaging interface, fundamentally changing how authenticity is communicated.
| Element | Legacy SMS | RCS Verified Sender |
|---|---|---|
| Sender Name | Easily spoofed | Pre-approved and registered |
| Brand Logo | Not supported | Official logo displayed |
| Verification Badge | None | Visible verified checkmark |
For users, the most immediate signal is the verified badge. Similar in concept to social platform verification marks, it indicates that the sender’s identity has been authenticated through formal review. An attacker may imitate a brand name textually, but cannot obtain the platform-issued verification status.
This dramatically raises the operational cost of impersonation. Fraudsters would need to bypass carrier-level onboarding controls, provide falsified corporate documentation, and survive ongoing compliance audits. That barrier is fundamentally different from simply registering a disposable SMS gateway account.
From a marketing perspective, this also transforms customer engagement. A verified RCS message can include structured cards, secure call-to-action buttons, and persistent brand identity elements. As industry analyses such as those referenced by GSMA note, trust directly impacts engagement rates. When users clearly see a validated sender, hesitation decreases and interaction quality improves.
Importantly, Verified Sender is not merely visual branding. It is part of a broader anti-abuse architecture that combines identity proofing, traffic monitoring, and revocation mechanisms. If a registered sender violates policies or exhibits suspicious behavior, access can be suspended—something impossible in the open SMS spoofing environment.
In practical terms, brand impersonation moves from being technically trivial to institutionally constrained. That shift marks a structural evolution in mobile messaging security.
For security-conscious users and data-driven marketers alike, the implication is clear: RCS Business Messaging with Verified Sender does not just filter fraud after the fact. It redesigns the communication channel so that authenticity is embedded at the protocol level, making large-scale brand spoofing far more difficult to execute.
End-to-End Encryption in RCS and Its Security Implications
End-to-end encryption in RCS fundamentally changes the trust model of mobile messaging. Unlike legacy SMS, which travels largely in plaintext within carrier networks, modern RCS chats in Google Messages are protected by end-to-end encryption by default when both parties use compatible clients. This means that only the sender and recipient can read the content, while carriers, intermediaries, and even the platform provider cannot decrypt it.
This architectural shift dramatically reduces the risk of interception, lawful or unlawful, at the transport layer. In the SMS era, vulnerabilities in signaling systems such as SS7 exposed structural weaknesses that could be abused for message interception. With RCS over IP and E2EE applied at the application layer, the attack surface moves away from the core network and toward endpoint security.
| Aspect | SMS | RCS with E2EE |
|---|---|---|
| Message visibility | Readable within carrier network | Readable only on endpoints |
| Interception risk | Network-level exposure possible | Cryptographically protected |
| Integrity protection | Limited | Tamper detection built-in |
According to Google’s security documentation, encrypted RCS conversations are processed on-device for spam and scam detection, ensuring that protective AI features do not require server-side message inspection. This design reflects a privacy-by-default philosophy, where metadata may inform abuse prevention, but message bodies remain inaccessible to the provider.
However, encryption also introduces nuanced security implications. When messages are cryptographically sealed, centralized content moderation becomes technically constrained. This creates tension between privacy and abuse mitigation. Industry discussions, including those referenced in GSMA materials, emphasize that user reporting mechanisms and device-level intelligence must compensate for the reduced visibility at the network layer.
It is also critical to distinguish between person-to-person RCS chats and business messaging. In many RCS Business Messaging scenarios, end-to-end encryption may not apply in the same way, because enterprises require message processing for automation, archiving, or compliance. Users therefore benefit from understanding whether a conversation is E2EE-protected, typically indicated within the messaging interface.
From a threat-model perspective, E2EE neutralizes passive eavesdropping and large-scale bulk interception. Yet it does not inherently prevent social engineering, device compromise, or screenshot-based data leakage. If malware infects an endpoint, encrypted transport offers no protection once the message is decrypted locally. This is why Google combines E2EE with on-device machine learning and Safe Browsing protections rather than relying on cryptography alone.
For security-conscious users, the practical implication is clear: enabling RCS and verifying that chats are encrypted provides a measurable upgrade over SMS. But true resilience emerges only when encryption is paired with secure hardware, regular OS updates, and strong authentication practices. In the evolving landscape of mobile threats, E2EE in RCS is not merely a feature—it is a structural redefinition of how trust is enforced in everyday communication.
Carrier Strategies in Japan: +Message, Google Jibe, and Rakuten Link
Japan’s messaging landscape is uniquely complex, shaped by strong carrier influence, high iPhone penetration, and the long-standing dominance of LINE. Within this environment, three approaches define today’s carrier strategies: +Message by the major telcos, Google Jibe–based RCS deployment, and Rakuten Link’s independent ecosystem.
Each reflects a different philosophy about control, interoperability, and security. For gadget enthusiasts and power users, understanding these differences directly impacts how well you are protected from smishing and spoofed business messages.
+Message: Telco-Led RCS with Domestic Focus
Launched in 2018 by NTT Docomo, KDDI, and SoftBank, +Message is based on the GSMA’s RCS standard and was designed as a carrier-native alternative to OTT apps. It supports rich media, group chat, and official accounts, positioning itself as a trusted channel for banks, municipalities, and utilities.
From a security standpoint, its official account framework reduces impersonation risk. Enterprises must register and undergo screening before distributing branded messages. This mirrors the Verified Sender concept described by Google for RCS Business Messaging.
However, +Message historically faced structural limitations. Early interoperability constraints, MVNO compatibility issues, and the need for a dedicated app installation slowed adoption. In a market where friction determines usage, that mattered.
Google Jibe: Global Infrastructure Meets Japanese Carriers
KDDI’s decision to adopt Google’s Jibe Cloud marked a strategic shift. Instead of operating a fully isolated domestic RCS stack, KDDI aligned with Google’s global RCS backend, enabling tighter integration with Google Messages and its AI-driven spam detection.
| Aspect | +Message (Telco Stack) | Google Jibe Integration |
|---|---|---|
| Backend Control | Carrier-managed | Google cloud infrastructure |
| Spam Intelligence | Primarily domestic data | Global-scale AI signals |
| Interoperability | Japan-centric rollout | Universal Profile ecosystem |
This move effectively connected Japanese Android users to Google’s worldwide spam intelligence network. As Google explains in its security documentation, spam detection leverages aggregated, privacy-preserving signals across massive user bases. That scale matters when facing rapidly evolving AI-generated scams.
For users, the practical impact is subtle but powerful: RCS becomes native within Google Messages, and carrier boundaries become less visible. Security improvements arrive through app updates rather than carrier-specific feature rollouts.
Rakuten Link: Vertical Integration with Trade-Offs
Rakuten Mobile took a different path. Rakuten Link functions as an app-centric communication layer tied closely to its network strategy, including free domestic calls and messaging incentives. This vertical integration supports aggressive customer acquisition.
Yet security capabilities depend heavily on Rakuten’s own filtering mechanisms rather than Google Messages’ full AI stack. That means spam detection performance may differ depending on whether messages are handled within Rakuten Link or via standard SMS fallback.
As iOS 18 expands RCS support and cross-platform messaging improves, carrier strategies are converging toward interoperability. The competitive axis is shifting from feature parity to trust, verification, and AI-backed protection.
For tech-savvy users, the takeaway is strategic rather than cosmetic: selecting a carrier today also means selecting an underlying RCS infrastructure—and with it, a specific security architecture.
iOS 18 and RCS Adoption: Cross-Platform Security Breakthrough
The arrival of iOS 18 with native support for RCS Universal Profile marks a structural shift in mobile messaging security. For the first time, iPhone and Android devices can exchange rich messages over a standardized IP-based protocol instead of falling back to legacy SMS. This change is not just about better photos or read receipts. It directly affects how cross-platform fraud and spoofing are mitigated.
According to GSMA specifications and industry analyses such as those summarized by Vonage, RCS introduces identity validation and transport-level improvements that SMS never had. When iOS 18 enables RCS by default, the weakest link in many cross-device conversations—unencrypted, unauthenticated SMS fallback—begins to disappear.
| Feature | Legacy SMS (iOS–Android) | RCS on iOS 18 & Android | Security Impact |
|---|---|---|---|
| Transport | SS7 signaling | IP data channel | Reduced exposure to SS7 abuse |
| Sender Identity | Easily spoofed | Profile-based validation | Harder impersonation |
| Encryption | Not end-to-end | Protocol-level protection | Improved confidentiality |
| Rich UI | Text only | Brand elements supported | Visual trust signals |
One of the most important breakthroughs is the normalization of verified business messaging across platforms. Google’s RCS Business Messaging framework requires vetting before brands can display official names and logos. With iOS 18 participating in the same Universal Profile ecosystem, the security model no longer fragments by operating system. A verified sender on Android can now present consistent identity signals to iPhone users as well.
This dramatically raises the cost of large-scale impersonation attacks. Under SMS, attackers could spoof alphanumeric sender IDs with minimal friction. Under RCS, brand registration, number ownership validation, and platform-level approval act as gatekeepers. As documented in Google’s developer materials on Verified SMS and RCS Business Messaging, the process involves proof of legal entity and control over sending infrastructure.
Encryption dynamics also evolve. While implementation details differ, RCS enables stronger message protection compared to plaintext SMS transmission within carrier networks. For consumers, this reduces interception and tampering risks in cross-platform conversations. For enterprises, it creates a more secure baseline for transactional messaging such as delivery notifications or authentication prompts.
There is also a behavioral security effect. When users consistently see typing indicators, high-resolution media, and branded profiles in legitimate conversations, low-fidelity SMS phishing attempts become easier to spot. Security researchers often emphasize that trust signals influence user judgment. By aligning the user experience across iOS and Android, RCS reduces the visual ambiguity that scammers exploit.
Of course, RCS is not a silver bullet. Analysts have noted concerns that richer channels can also be abused if verification is weak. However, the cross-platform adoption triggered by iOS 18 shifts the default communication path toward a protocol designed with identity and extensibility in mind. That alone narrows the attack surface that legacy SMS left wide open for decades.
The real breakthrough is not feature parity but security parity. When the majority of iPhone and Android devices communicate through the same modern standard, the ecosystem can coordinate defenses at scale. In practical terms, fewer conversations silently downgrade to insecure SMS, and more interactions benefit from authentication, encryption, and structured sender validation.
For gadget enthusiasts and security-conscious users, iOS 18’s RCS adoption represents a long-awaited convergence. It transforms cross-platform messaging from a fragmented compromise into a unified, more trustworthy channel—one where protocol-level design finally supports the expectations of a post-SMS security era.
Government Action and Opt-In Regulation: Legal Pressure on SMS Abuse
As SMS abuse has evolved into a high-yield criminal business, governments have shifted from reactive warnings to structural intervention. In Japan, the Ministry of Internal Affairs and Communications has formally requested stronger anti-phishing measures from carriers, signaling that spam control is no longer optional but a matter of public policy.
According to official communications from the ministry, operators are expected to enhance filtering, improve sender verification, and cooperate in rapid information sharing when large-scale smishing campaigns are detected. This represents a move from voluntary best practice to coordinated regulatory pressure.
The legal backbone of this approach lies in opt-in regulation. Under the Act on Regulation of Transmission of Specified Electronic Mail and related frameworks, businesses are prohibited from sending promotional SMS without prior consent from recipients.
| Requirement | Legal Expectation | Security Impact |
|---|---|---|
| Prior consent (Opt-in) | Explicit user agreement before sending ads | Reduces unsolicited bulk messaging |
| Clear sender identification | Business name must be stated | Limits anonymous abuse |
| Easy opt-out | Immediate stop via simple action | Prevents persistent harassment |
| Record retention | Proof of consent must be stored | Enables enforcement and audits |
The opt-in principle is particularly powerful in the SMS ecosystem because distribution channels are concentrated among a limited number of carriers and aggregators. When regulators require proof of consent logs, non-compliant messaging providers risk contract termination. This creates upstream pressure that squeezes out gray-zone operators before messages even reach end users.
Moreover, the ministry has encouraged the adoption of authentication mechanisms such as DMARC in the broader messaging environment. While originally designed for email, its philosophy—domain-level authentication and rejection policies—reinforces the same idea: only verifiable senders should be allowed to reach consumers at scale.
From a marketing perspective, this regulatory tightening forces a strategic pivot. Growth can no longer rely on purchased lists or ambiguous consent banners. Brands must design transparent onboarding flows, log consent events precisely, and provide frictionless unsubscribe mechanisms. Compliance is no longer just legal hygiene; it becomes a trust asset.
For security-conscious gadget enthusiasts, this shift is significant. Technical defenses such as AI spam filters operate at the edge, but opt-in regulation works at the source. By legally shrinking the pool of legitimate bulk senders, authorities reduce the camouflage criminals exploit. The battlefield is no longer limited to algorithms—it now includes contractual liability, audit trails, and enforcement leverage.
In short, government action transforms SMS from an open broadcast channel into a permission-based medium. That structural change, more than any single filter or app setting, is what raises the cost of abuse and reshapes the economics of smishing in 2025.
Advanced Defense Strategies for Power Users: Passkeys, Authenticator Apps, and Layered Protection
For power users, basic spam filtering is not enough. If attackers are leveraging AI, fake base stations, and social engineering, your defense must evolve beyond SMS-based authentication and single-layer protection.
The most critical shift is moving away from SMS as a security backbone. As repeatedly highlighted by security experts contributing to FIDO and public policy discussions in Japan, SMS was never designed to be a strong authentication channel.
If your most sensitive accounts still rely on SMS one-time passwords, you are defending a 2026 threat landscape with a 1990s protocol.
Why Passkeys Are the Strategic Upgrade
Passkeys, backed by the FIDO Alliance and implemented by Google, Apple, and Microsoft, replace passwords and SMS OTPs with cryptographic key pairs stored securely on your device.
Authentication requires biometric verification or device unlock, and the private key never leaves your hardware. This architecture eliminates phishing because there is no shared secret to steal.
According to FIDO-based security frameworks referenced in policy discussions around Japan’s digital authentication reforms, passkeys fundamentally neutralize credential harvesting and OTP interception attacks.
| Method | Phishing Resistant | Dependent on SMS |
|---|---|---|
| SMS OTP | No | Yes |
| Authenticator App (TOTP) | Partially | No |
| Passkeys (FIDO) | Yes | No |
For high-value services such as financial platforms, cloud storage, and domain registrars, enabling passkeys should be your default strategy wherever supported.
Authenticator Apps as an Interim Layer
Where passkeys are not yet available, migrate from SMS OTP to app-based authenticators such as Google Authenticator or hardware-backed tokens.
Time-based One-Time Passwords (TOTP) are generated locally on your device and are not transmitted through carrier networks, making them immune to fake base station interception.
This single settings change removes an entire class of smishing-driven account takeover risk.
Layered Protection: Defense in Depth for Messaging
Advanced users should combine protocol upgrades with intelligent filtering. Google Messages’ on-device machine learning and Safe Browsing URL screening provide contextual and link-level analysis without exposing private content to the cloud.
Complementing this with reputation-based tools such as community-driven caller databases creates a dual-layer model: AI detects behavioral anomalies, while databases block known malicious numbers.
This mirrors enterprise security architecture, where endpoint detection and threat intelligence feeds operate simultaneously.
Finally, regularly auditing your account security settings is essential. Review which services still allow SMS recovery, disable it where alternatives exist, and ensure your primary email account itself is protected by passkeys or hardware-based authentication.
In a threat environment shaped by AI-generated deception and infrastructure-level attacks, proactive configuration is your strongest advantage.
Power users do not wait for scams to be detected. They redesign their authentication surface so the scam no longer works.
参考文献
- Google Security Blog:New AI-Powered Scam Detection Features to Help Protect You on Android
- Google Support:How Google protects your privacy with spam detection – Google Messages
- Commsrisk:Japanese Telcos Warn Public about Smishing Messages from Fake Base Stations
- Keepnet Labs:Smishing Statistics: SMS Phishing Trends & Stats (Updated 2025 Sep)
- GSMA:KDDI: SMS phishing countermeasures – Scams
- Google for Developers:An introduction to Verified SMS & RCS Business Messaging
- Wikipedia:Rich Communication Services
